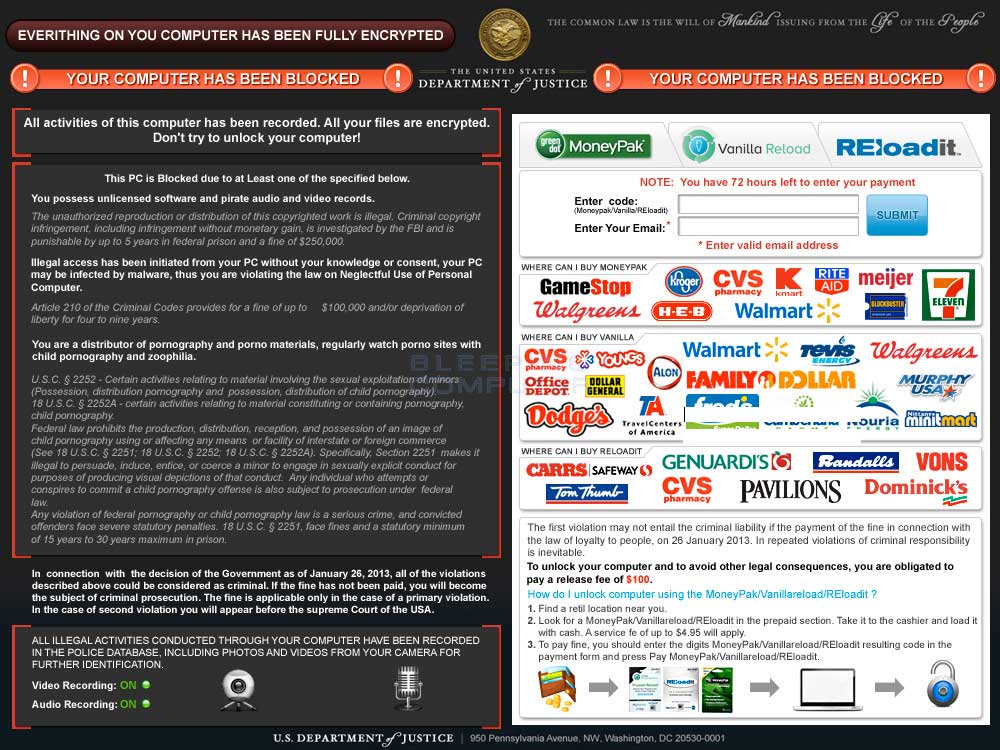
The Everything on your computer has been fully encrypted Ransomware or Your Computer has been Blocked Ransomware are computer infections from the Trojan:Win32/Harasom.A Ransomware family that prevent you from accessing your Windows desktop, files, or applications until you pay a $100 or $300 ransom to the malware developers. This ransomware pretends to be a lock screen placed on your computer by the Department of Justice due to illegal activities being detected on your computer. It then states that you must pay a fine of $100 using a MoneyPak, Vanilla Reload, or Reloadit voucher or you will face legal prosecution. Please remember that this is a computer infection and not a legitimate message from any government agency.
This infection will also encrypt any files that have the follow extensions: .ddrw, .pptm, .dotm, .xltx, .text, .docm, .djvu, .potx, .jpeg, .pptx, .sldm, .lnk, .txt, .xlsm, .sldx, .xlsb, .ppam, .xlsx, .ppsm, .ppsx, .docx, .odp, .eml, .ods, .dot, .php, .xla, .pas, .gif, .mpg, .ppt, .bkf, .sda, .mdf, .ico, .dwg, .mbx, .sfx, .mdb, .zip, and .xlt. When encrypting these files, the infection will rename them as HTML files. If you attempt to open one of these files, your web browser will open and show you a picture of the lock screen that states that the file is encrypted. Thankfully, Emsisoft has created a program that can decrypt these files and remove the infection as shown in the removal guide below.The text of the lock screen for this variant of the Trojan:Win32/Harasom.A Ransomware family is:
The United States Department of Justice
The common law is the will of mankind issuing from the life of the people.Everything on your computer has been fully encrypted.
Your computer has been blocked!All activities of this computer has been recorded. All your files are encrypted. Don't try to unlock your computer.
This PC is blocked due to at Least one of the specified below.
You possess unlicensed software and pirate audio and video records.
<Fake legalese here>
Illegal access has been initiated from your PC without your knowledge or consent, your PC may be infected by malware, thus you are violating the law on Neglectful Use of Personal Computer.
<Fake legalese here>
Your are a distributor of pornography and porno materials, regularly watch porno sites with child pornography and zoophilia.
<Fake legalese here>
In connection with the decision of the Government as of January 26, 2013, all of the violations described above could be considered criminal. If the fine has not been paid, you will become the subject of criminal prosecution. The fine is applicable only in the case of a primary violation. In the case of second violation you will appear before the Supreme Court of the USA.
ALL ILLEGAL ACTIVITIES CONDUCTED THROUGH YOUR COMPUTER HAVE BEEN RECORDED IN THE POLICE DATABASE, INCLUDING PHOTOS AND VIDEOS FROM YOUR CAMERA FOR FURTHER IDENTIFICATION.
To unlock your computer and avoid other legal consequences, you are obligated to pay a release fee of $100.
As you can see, this is a computer infection and not a legitimate message from the United States Department of Justice. Therefore, ignore anything it displays and instead use the removal guide below to remove the Your Computer has been Blocked ransomware from your computer.
Everything on your computer has been fully encrypted Ransomware Removal Options
Self Help Guide
If you are uncomfortable making changes to your computer or following these steps, do not worry! Instead you can get free one-on-one help by asking in the forums.
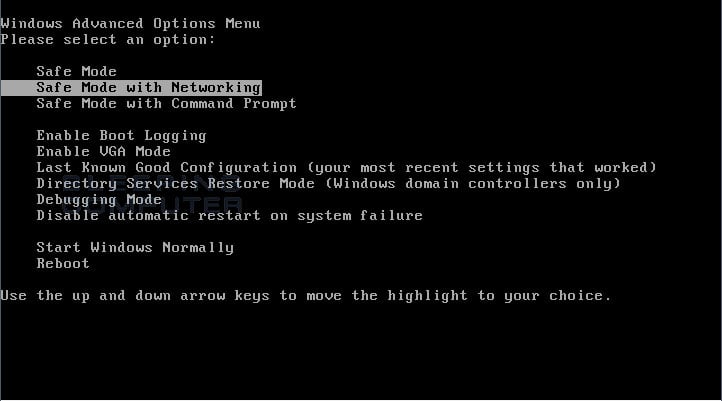
- Print out these instructions as we will need to reboot your computer into Safe mode with Networking and you may not have access to your web browser for part of this process.
- This infection makes it difficult to access your documents and programs because it locks the screen. In order to bypass this locker, we need to reboot into Safe Mode with Networking. To
do this, perform the following steps for your version of Windows:
Windows 8: Please follow the steps in this guide to restart your computer in Windows 8 Safe Mode.
Windows XP, Vista, and 7: Turn your computer off and then back on and when you see anything on the screen, immediately start tapping the F8 key on your keyboard. Eventually you will be brought to a menu similar to the one below:
Using the arrow keys on your keyboard, select Safe Mode with Networking and press Enter on your keyboard. If you are having trouble entering safe mode, then please use the following tutorial:
How to start Windows in Safe Mode
Windows will now boot into safe mode with networking and prompt you to login as a user. - When you are prompted to login, please login as the user that is infected with
Everything on your computer has been fully encrypted Ransomware.
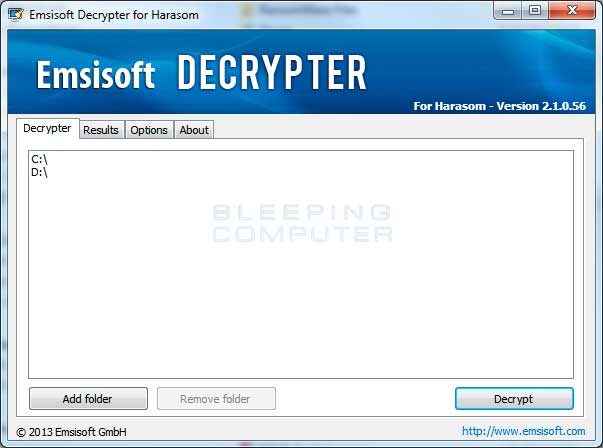
- Now download and save the Emsisoft Harasom Decrypter to your desktop from the link below:
http://tmp.emsisoft.com/fw/decrypt_harasom.exe - Once the file has been downloaded, double-click on the decrypt_harasom.exe icon to start the program. If Windows Smart Screen issues an alert, please allow the program to run anyway.
- When the Decrypter starts you will be shown a screen showing all of the drives detected on your computer as seen in the image below.

To start the decryption process, please click on the Decrypt button. - The Emsisoft Harasom Decrypter will now scan your computer for variants of the Harasom infection and quarantine them. If it detects any encrypted files it will decrypt them and save them in their original location. You can see an image of the Emsisoft Harasom Decrypter scanning a computer below.

When it has finished, please review the results and then close the program. - You can now check your data and if it opens properly, delete the encrypted versions found on your hard drive.
- As this infection is known to be installed by vulnerabilities in out-dated and insecure programs, it is strongly suggested that you use
Secunia PSI to scan for vulnerable programs on your computer. A tutorial on
how to use Secunia PSI to scan for vulnerable programs can be found here:
How to detect vulnerable and out-dated programs using Secunia Personal Software Inspector
Your computer should now be free of the Trojan:Win32/Harasom.A infection. If your current anti-virus solution let this infection through, you may want to consider purchasing the full version of Emsisoft Anti-malware to protect your computer against these types of threats in the future.