
Today, researchers have responsibly disclosed a security vulnerability by exploiting which they could access over 100,000 private employee records of United Nations Environmental Programme (UNEP).
The data breach stemmed from exposed Git directories and credentials, which allowed the researchers to clone Git repositories and gather a large amount of personally identifiable information (PII) associated with UNEP employees.
Git directory exposed WordPress DB and Git credentials
Ethical hacking and security research group Sakura Samurai have now disclosed their findings on a vulnerability that let them access over 100,000 private records of United Nations Environment Programme (UNEP) employees.
The documents and screenshots shared with BleepingComputer provide extensive details on the nature of this security flaw and all that it exposed.
Having come across the United Nation's Vulnerability Disclosure Program and InfoSec Hall of Fame, researchers Jackson Henry, Nick Sahler, John Jackson, and Aubrey Cottle of Sakura Samurai set out to hunt for any security flaws impacting UN systems.
They then came across exposed Git directories (.git) and Git credential files (.git-credentials) on domains associated with the UNEP and United Nation's International Labour Organization (ILO).
The researchers were able to dump the contents of these Git files and clone entire repositories from the *.ilo.org and *.unep.org domains using git-dumper.
The .git directory contents comprised sensitive files, such as WordPress configuration files (wp-config.php) exposing the administrator's database credentials.
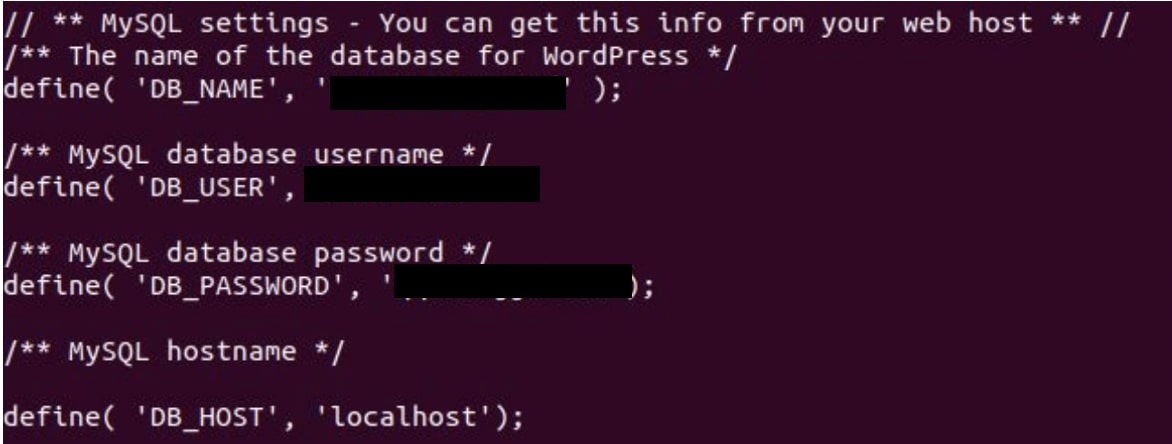
Source: Sakura Samurai
Likewise, different PHP files exposed as a part of this data breach contained plaintext database credentials associated with other online systems of the UNEP and UN ILO.
In addition, the publicly accessible .git-credentials files enabled the researchers to get their hands on UNEP's source code base.
Exfiltrated data contains over 100,000 employee records
Using these credentials, researchers were able to exfiltrate over 100,000 UN employee records from multiple systems.
The data set obtained by the group exposed travel history of UN staff, with each row containing: Employee ID, Names, Employee Groups, Travel Justification, Start and End Dates, Approval Status, Destination, and the Length of Stay.
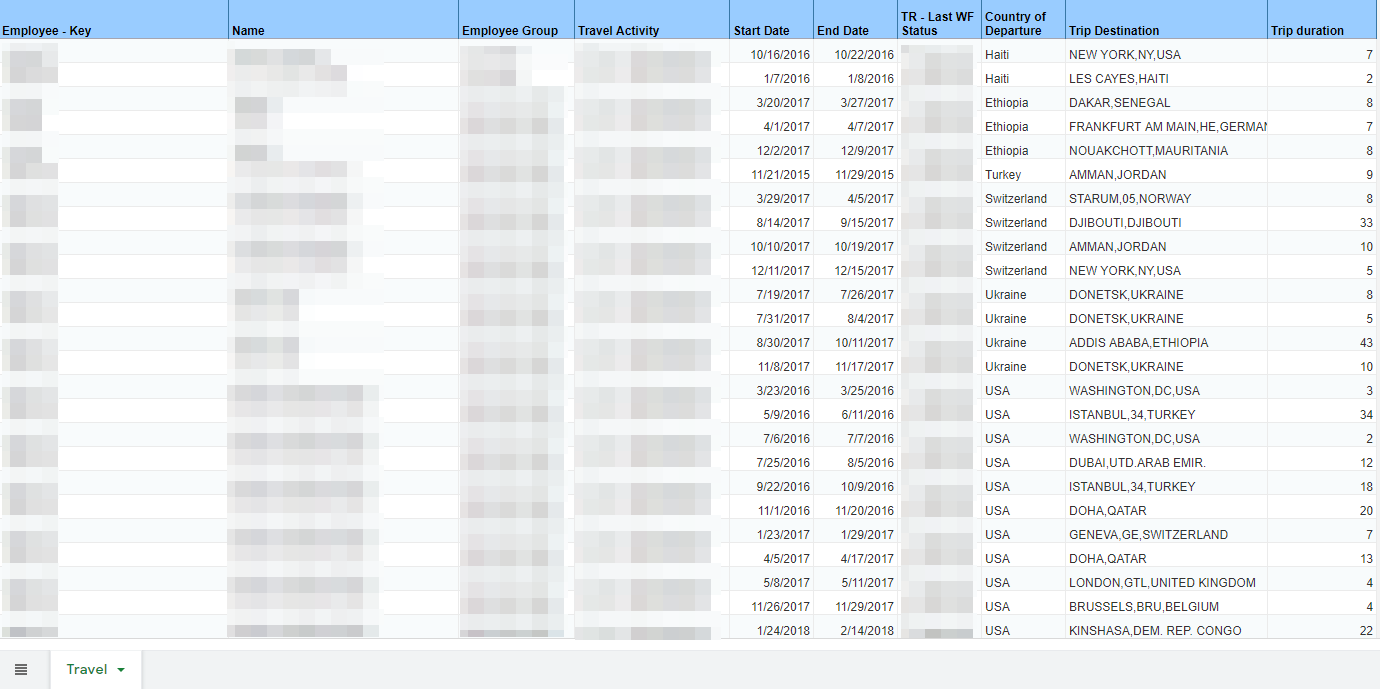
Source: Sakura Samurai
Likewise, other UN databases accessed by the researchers as a part of their analysis exposed HR demographic data (nationality, gender, pay grade) on thousands of employees, project funding source records, generalized employee records, and employment evaluation reports.
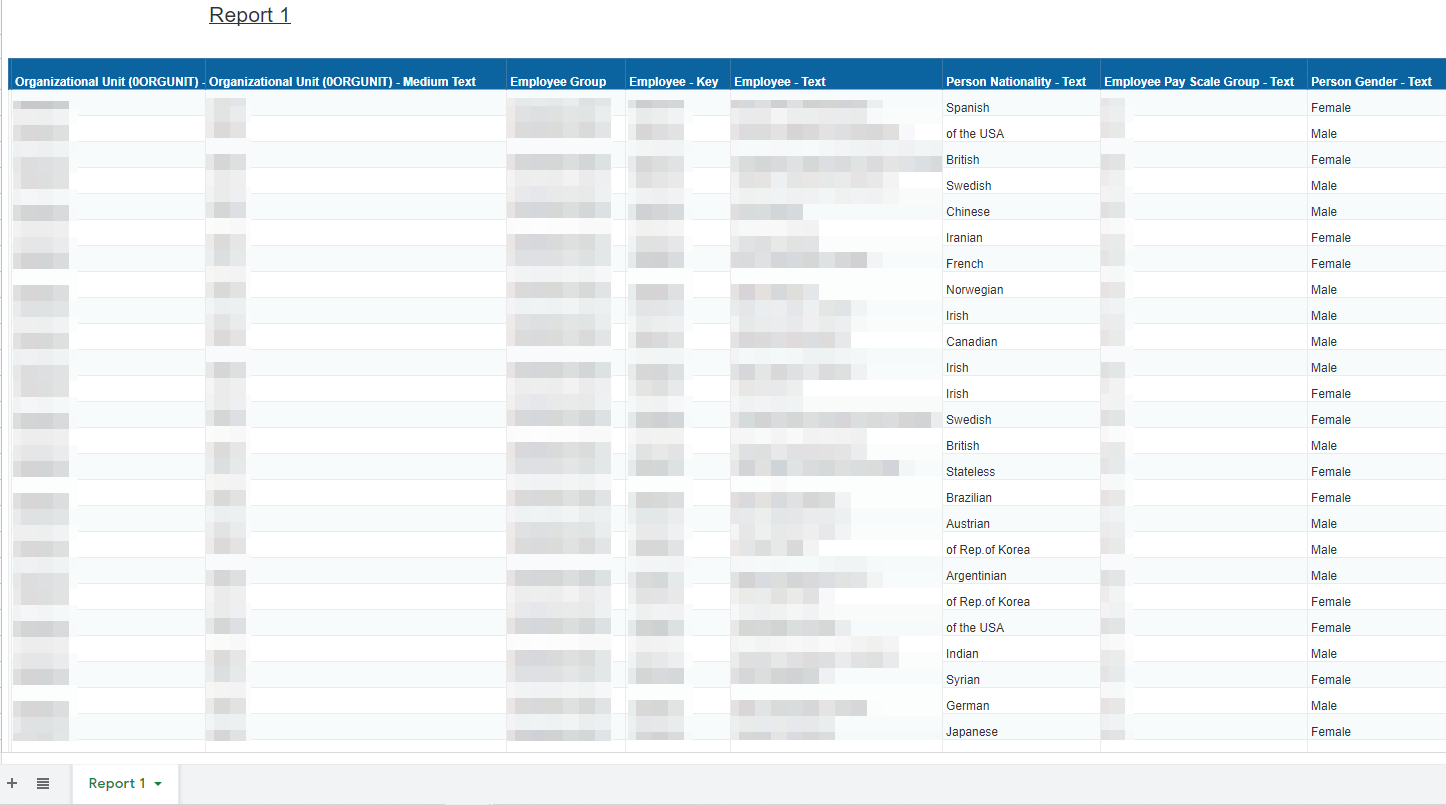
Source: Sakura Samurai
In an email interview with BleepingComputer, the group said:
"When we started researching the UN, we didn't think it would escalate so quickly. Within hours, we already had sensitive data and had identified vulnerabilities. Overall, in less than 24 full hours we obtained all of this data," Sakura Samurai told BleepingComputer.
"In total, we found 7 additional credential-pairs which could have resulted in unauthorized access of multiple databases. We decided to stop and report this vulnerability once we were able to access PII that was exposed via Database backups that were in the private projects," state the researchers in their blog post.
Threat actors likely already accessed the data
The researchers shared a series of emails with BleepingComputer that showed they had originally reported the vulnerability to UN privately on January 4th, 2021.
UN Office of Information and Communications Technology (OICT) initially acknowledged their report, but, without realizing the vulnerability concerned UNEP, responded:
"The reported vulnerability does not pertain to the United Nations Secretariat, and is for ILO (International Labour Organization)," according to the emails seen by BleepingComputer, and something the UN is known to do in the past.
Eventually, according to these emails, Saiful Ridwan, Chief of Enterprise Solutions at UNEP thanked the researchers for their vulnerability report while stating that their DevOps team had taken immediate steps to patch the vulnerability and that an impact assessment of this vulnerability was in progress.
Further, in a follow-up email to researchers, seen by BleepingComputer, UNEP stated that a data breach disclosure notice was in the works but that it was "challenging as we have not done this before."
Overall, the researchers told BleepingComputer, United Nations was quick to patch this security issue within under a week.
"Honestly, I commend Saiful for the quick fixes. Even though he stated that this was fairly new to him, they patched in record speed and secured the data."
"At this point, our only concern is informing the affected users. Particularly, Aubrey Cottle A.K.A. Kirtaner had noted that if it was this easy to obtain the data, threat actors likely already have the data."
"The group was in agreement that the UNEP should analyze the trajectory of the exposed PII to determine how many threat actors, if any, have the data," Sakura Samurai founder John Jackson told BleepingComputer.
This is not the first time UN systems have suffered a data breach.
In 2019, the UN did not disclose a cyberattack that had severely compromised their networks and databases.
In 2020, a disclosure finally came out from the UN which pinned the blame for the hack on a SharePoint vulnerability.
UNEP: no signs of additional unauthorized access
BleepingComputer reached out to UNEP for comment and we were initially told, "Thank you for informing us about this issue. We are contacting our experts and colleagues and we will revert as soon as we have the relevant information."
On January 15th, 2021, a UNEP spokesperson shared more information with BleepingComputer:
"Upon notification of the breach on 4 January 2021, the vulnerability was addressed within 12 hours. The breached data includes over 100,000 lines of information, including HR and travel details dating from 2015 to 2018."
"UNEP is not aware of additional unauthorized access to the information nor any misuse of the data. The dataset does not contain information that could be used to attack any other UN data or IT systems."
"This breach was reported to the United Nations through an established Information Security 'Hall of Fame' ethical hacking programme. This programme allows the public to assist in the protection of ICT resources through finding and disclosing vulnerabilities in the UN's publicly-accessible information system."
"UNEP is working with UN Secretariat cybersecurity experts to address the data breach and strengthen its IT security," a UNEP spokesperson told BleepingComputer.
Update 11-Jan-2021: Clarified 100,000 employee records were accessed as a part of the breach.
Update 15-Jan-2021: Added statement from UNEP.


Comments
premomh - 3 years ago
UNEP has 100k employees? For an organization that is run off various government (mainly USA) handouts, that's a little ridiculous, no?
Observer3 - 3 years ago
Hi premomh,
please have a look. It says: 100'000 RECORDS that have been leaked and under the second screenshot that the organisation has a bit more than 7000 employees (which includes staff as well as short term contractors). The US funding was indeed big until 1995 and has since been mainly fed by contributions from European Governments.
premomh - 3 years ago
The article states: "Exfiltrated data of over 100,000 employees". Search it. Or just look. Second major headline/section line...
Either way, 7 employees would be too many...
EDIT - and btw - United States was funding 27.89% of the UN's budget as of 2019... (which is more than the top 5 European countries combined). So.. yeah.
P.S. I'm using the UN's own numbers... https://peacekeeping.un.org/en/how-we-are-funded
AxSharma - 3 years ago
Thank you. Have clarified that 100,000 UNEP employee *records* were accessed during the breach.
premomh - 3 years ago
Even though it wasn't necessarily intentional :) I'm glad I helped. Thank You!