
Two vulnerabilities impacting the POST SMTP Mailer WordPress plugin, an email delivery tool used by 300,000 websites, could help attackers take complete control of a site authentication.
Last month, security researchers Ulysses Saicha and Sean Murphy discovered two vulnerabilities in the plugin and reported them to the vendor via Wordfence's bug bounty program.
The first, tracked as CVE-2023-6875, is a critical authorization bypass flaw arising from a “type juggling” issue on the connect-app REST endpoint. The issue impacts all versions of the plugin up to 2.8.7
An unauthenticated attacker could exploit it to reset the API key and view sensitive log information, including password reset emails.
Specifically, the attacker can exploit a function relating to the mobile app to set a valid token with a zero value for the authentication key via a request.
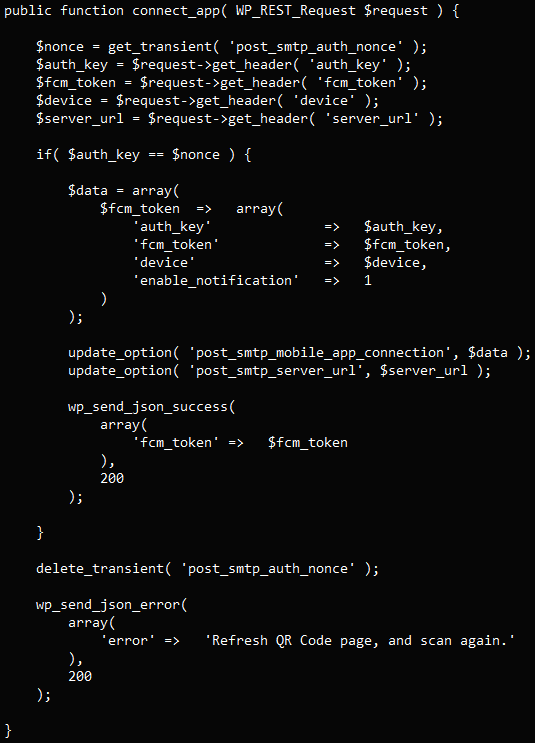
Next, the attacker triggers a password reset for the site's admin and then accesses the key from within the application, changing it and locking the legitimate user out of the account.
With administrator privileges, the attacker has full access and can plant backdoors, modify plugins and themes, edit and publish content, or redirect users to malicious destinations.
The second vulnerability, is a cross-site scripting (XSS) problem identified as CVE-2023-7027 that arises from insufficient input sanitization and output escaping.
The flaw impacts POST SMPT up to version 2.8.7 and could let attackers inject arbitrary scripts into the web pages of the affected site.
Wordfence first contacted the vendor about the critical flaw on December 8, 2023, and after submitting the report they followed up with a proof-of-concept (PoC) exploit on December 15.
The XSS issue was reported on December 19, 2023, and a PoC was shared the next day.
The plugin’s vendor published on January 1, 2024 version 2.8.8 of POST SMPT that includes security fixes for both issues.
Based on statitics from wordpress.org, there are roughly 150,000 sites that run a vulnerable version of the plugin that is lower than 2.8. From the remaining half that have version 2.8 and higher installed, thousands are likely vulnerable as well when considering that the platform reports roughly 100,000 downloads since the release of the patch.


Comments
PluginVulns - 3 months ago
There is a lot wrong with this story. Please talk to a second source before running stories like this. Get in touch with us. We would be happy to help you.
The mentioned researchers don’t work for Wordfence.
The feature at issue didn’t even exist in the plugin until version 2.7.0, so versions earlier than that couldn’t be vulnerable and so your count of the affected websites is likely way off.
The CVE record is also wrong, as it says “all versions up to, and including, 2.8.7” are vulnerable, which isn’t right. Maybe you could cover the inaccuracy of CVE’s information. The source for that information, Wordfence, doesn’t actually determine what versions are even vulnerable, so that couldn’t be reliable information.
You could also cover that the developer of this plugin has offloaded responding to security issues to a third-party security provider, Patchstack, which isn’t make sure that security issues are being addressed: https://www.pluginvulnerabilities.com/2023/09/08/plugin-that-is-part-of-patchstacks-vulnerability-disclosure-program-vdp-still-contains-publicly-disclosed-sql-injection-issue/