
Hackers are actively exploiting a recently fixed vulnerability in the WordPress Advanced Custom Fields plugin roughly 24 hours after a proof-of-concept (PoC) exploit was made public.
The vulnerability in question is CVE-2023-30777, a high-severity reflected cross-site scripting (XSS) flaw that allows unauthenticated attackers to steal sensitive information and escalate their privileges on impacted WordPress sites.
The flaw was discovered by website security company Patchstack on May 2nd, 2023, and was disclosed along with a proof-of-concept exploit on May 5th, a day after the plugin vendor had released a security update with version 6.1.6.
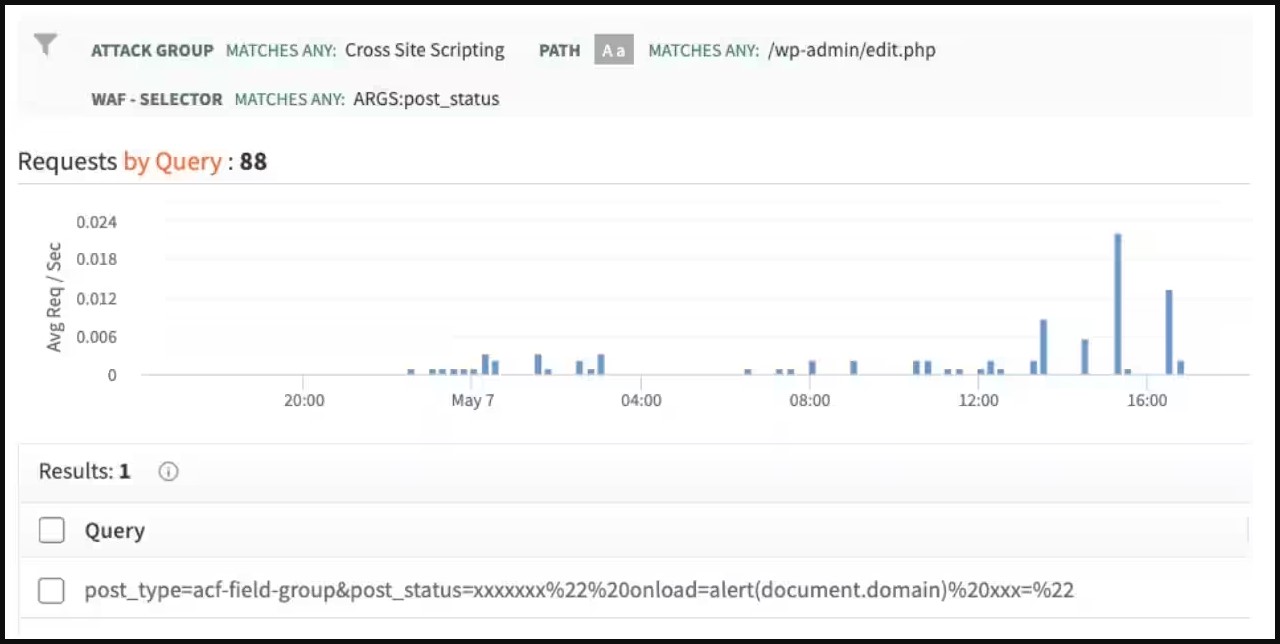
As the Akamai Security Intelligence Group (SIG) reported yesterday, starting May 6th, 2023, they observed significant scanning and exploitation activity using the sample code provided in Patchstack's write-up.
"The Akamai SIG analyzed XSS attack data and identified attacks starting within 24 hours of the exploit PoC being made public," reads the report.
"What is particularly interesting about this is the query itself: The threat actor copied and used the Patchstack sample code from the write-up."
Considering that over 1.4 million websites using the impacted WordPress plugin have not upgraded to the latest version, based on wordpress.org stats, the attackers have quite a large attack surface to explore.
The XSS flaw requires the involvement of a logged-in user who has access to the plugin to run malicious code on their browser that will give the attackers high-privileged access to the site.
The malicious scans indicate that this mitigation factor doesn't dishearten threat actors who trust that they can overcome it through basic trickery and social engineering.
Also, the exploit works on default configurations of the impacted plugin versions, which increases the chances of success for the threat actors without requiring extra effort.
WordPress site administrators using the vulnerable plugins are urged to immediately apply the available patch to protect from ongoing scanning and exploitation activity.
The recommended action is to upgrade 'Advanced Custom Fields' free and pro plugins to version 5.12.6 (backported) and 6.1.6.


Comments
PluginVulns - 11 months ago
With the vulnerability, a WordPress user logged in with the Administrator role would need to access a URL specified by an attacker and JavaScript code included in the URL would then run for them. So the requests that Akamai are claiming are happening wouldn’t do anything. It wouldn’t show if the vulnerability is present, as they claimed, since the attacker wouldn’t be logged in as an Administrator. Even if an Administrator accessed the URL, say, because they saw it in a log, it wouldn’t do anything malicious, it would just show an alert box for them.
This looks like a script kiddie that doesn’t understand the vulnerability and didn’t do any testing first, started trying the proof of concept on a wide-scale. That is pretty common. It doesn’t mean a vulnerability is under active exploit or will be, it just means that a lot of hackers are not competent.
It would help if you got at least a second source for stories, since claims made by security companies, like this one, are often not accurate.