Earlier this month we reported on an ongoing extortion email campaign that emailed recipients their password and stated hackers had recorded the them over their webcam while they visited adult sites.
Over the past week, scammers are now utilizing a new extortion email campaign that claims the recipient's phone was hacked, includes a partial phone number of the recipient, and further states that they created videos using the recipient's webcam. It then demands $1,000 USD in bitcoins or the hacker will release the video and other information.
This new campaign was brought to my attention last week by security researcher SecGuru who has seen thousands of these email being distributed.
New Sextortion Scam: "Your hacked phone + Phone number".
— SecGuru (@SecGuru_OTX) August 11, 2018
They now use telephone numbers, the telephone number is actually from the victim. Unfortunately people continue to pay :-( #extortion pic.twitter.com/1AHL4dt7x4
While the previous campaign utilized passwords found in data dumps from hacks, these emails instead use a partial phone number of the recipient. This information is used in the extortion emails to scare the recipient into thinking that the scammer actually hacked their phones and taken video of them through the phone's camera while they were on adult sites.
You can see the full text of one of these sextortion emails below.
Subject:(Part num your Hacked phone +XX XXXXXX5555)
It seems that, +XX XXXXXX5555, is your phone.
You may not know me and you are probably wondering why you are getting this e mail, right? actually, I setup a malware on the adult vids (porno) web-site and guess what, you visited this site to have fun (you know what I mean).
While you were watching videos, your internet browser started out functioning as a RDP (Remote Desktop) having a keylogger which gave me accessibility to your screen and web cam. after that, my software program obtained all of your contacts from your Messenger, FB, as well as email.
What did I do? I backuped phone. All photo, video and contacts. I created a double-screen video. 1st part shows the video you were watching (you've got a good taste haha . . .), and 2nd part shows the recording of your web cam. exactly what should you do?
Well, in my opinion, $1000 is a fair price for our little secret. You'll make the payment by Bitcoin (if you do not know this, search "how to buy bitcoin" in Google).
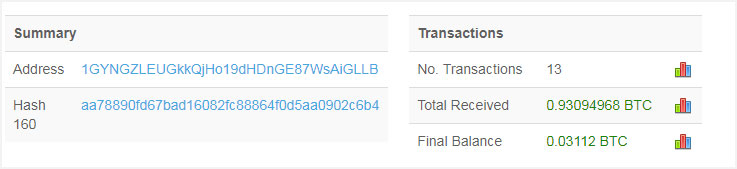
BTC Address: 1GYNGZLEUGkkQjHo19dHDnGE87WsAiGLLB
(It is cAsE sensitive, so copy and paste it)
Important: You have 48 hour in order to make the payment. (I've a unique pixel in this e mail, and at this moment I know that you have read through this email message). If I do not get the BitCoins, I will certainly send out your video recording to all of your contacts including relatives, coworkers, and so on. Having said that, if I receive the payment, I'll destroy the video immidiately. If you need evidence, reply with "Yes!" and I will certainly send out your video recording to your 6 contacts. It is a non-negotiable offer, that being said don't waste my personal time and yours by responding to this message.
According to SecGuru, we have now have four different sextortion email scam variants that are being distributed:
- Email without person identification
- Email with password
- Email with full name of the victim
- Email with phone number of the victim
Using account recovery to get partial phone numbers
SecGuru is not the only one who is seeing these scams. Didier Stevens, an ISC Handler, has also seen these emails and has confirmed that some of these partial numbers are accurate.
He also made an interesting observation.
While the previous campaign used data dumps from hacked sites to get passwords, Stevens feels that the partial phone numbers are not coming from the same types of sources.
"We don't know yet what source is used by the extortionists that provides email addresses with partial phone numbers, but I think it is unlikely to be a data breach (like with the password extortion emails). " Stevens said in a ISC handler diary post. "A classic data breach with phone numbers would contain full phone numbers, and I don't see why the extortionists would mask most of the digits."
Instead Stevens feels it may be possible that these partial numbers may be coming from password or account recovery forms such as the one from Gmail below.

With that said, there have been data leaks in the past that only contained partial numbers, so there is no definitive way to know where these numbers are coming from. What we do know, though, is that these sextortion scams generate a lot of money for the scammers.
Sextortion scammers raking in the moolah
The previous password extortion scam campaign made the scammers over $50k in one week. This new variant is also doing well.
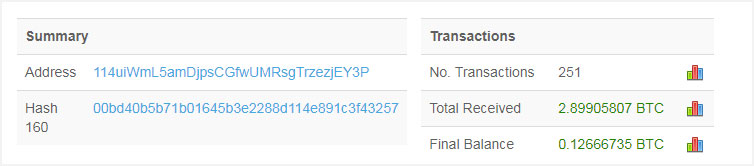
After looking at only two of the bitcoin addresses seen by SecGuru in these emails, we can see that people are falling for this scam and paying the requested bitcoins. For example, the address 114uiWmL5amDjpsCGfwUMRsgTrzezjEY3P has received 2.89905807 bitcoins, which at current prices is worth over $18,000, since July 11th. This address, though, may have been utilized in other previous variations of the scam.
Another bitcoin address associated with this scam is 1GYNGZLEUGkkQjHo19dHDnGE87WsAiGLLB and it has received 12 payments for a total of 0.93094968 since August 10th. This comes to a total of $5,800 USD earned over a 3 day period!
SecGuru has told BleepingComputer that he has many more emails to go through to tally the totals being earned through this campaign. If the above are any indication, though, it is a lot of money.


Comments
Perryg - 5 years ago
I received a similar email the other day and here is its contents:
It seems that, 3289, is your phone.
I setup a malware on the adult vids (porno) web-site and guess what, you visited this site to have fun (you know what I mean). While you were watching videos, your internet browser started out functioning as a Remote Desktop having a keylogger which gave me accessibility to your screen and web cam. after that, my software program obtained all of your contacts from your Messenger, FB, as well as email.
What did I do?
I backuped phone. All photo, video and contacts.
I created a double-screen video. 1st part shows the video you were watching (you've got a good taste haha . . .), and 2nd part shows the recording of your web cam.
exactly what should you do?
Well, in my opinion, $1000 is a fair price for our little secret. You'll make the payment by Bitcoin (if you do not know this, search "how to buy bitcoin" in Google).
BTC Address:
1Kq1ZqJHmduVgACjDQhCX4mPyyJkEUZytE
(It is cAsE sensitive, so copy and paste it)
Important:
You have 48 hour in order to make the payment. (I've a unique pixel in this e mail, and at this moment I know that you have read through this email message). If I do not get the BitCoins, I will certainly send out your video recording to all of your contacts including relatives, coworkers, and so on. Having said that, if I receive the payment, I'll destroy the video immidiately. If you need evidence, reply with "Yes!" and I will certainly send out your video recording to your 6 contacts. It is a non-negotiable offer, that being said don't waste my personal time and yours by responding to this message.
Angelo43 - 5 years ago
Hi, Every one
About the subject of this page:
I have to report and can serve as help and alert the following:
I have an email account on Yahoo.com with an indication of secondary email for recovery on Hotmail.com.
I lost my yahoo.com account password and for access to it I often type the last four numbers of my cell phone.
I received the pishing attempt described on the page in my secondary account from hotmail.com, including the last four numbers of my cell phone that I usually report on yahoo.com.
A year or a little longer, yahoo.com came to the public to report on data leaks that occurred on its platform.
I believe that this data helps to decipher how the hackers had access to the information of the four cell numbers and its modus operandi.
I do not know much about your English language, so I used google translator. I hope you're understandable.
Thanks
Conscriptspider - 5 years ago
For <email redacted by me> & copy to Detective
As you may have noticed, I sent last digits your phonenumberXxx88. I've been watching you for a few months now.
The fact is that you were infected with malware through an adult site that you visited. If you are not familiar with this, I will explain. Trojan Virus gives me full access and control your devices. This means that I can see everything on your screen, turn on the camera and microphone, but you do not know about it. I also have access to all your contacts and all your correspondence.
Why your antivirus did not detect malware? @nswer: My malware uses the driver, I update its signatures every 4 hours so that your antivirus is silent. I made a video showing h0w you satisfy yourself in the left half of the screen, and in the right half you see the video that you watched.
With one click of the m0use, I can send this vide0 to all your emails and contacts^. If you want to prevent this, transfer the amount of $732 to my bitcoin* @ddress (if you do not kn0w how to do this, write to Google: "Buy Bitcoin"). My bitcoin @ddress (BTC Wallet) is: 13FDEoFSZFYWmPd64aEB6pU1tJJCC7jb7N
After receiving the payment, I will delete the video and you will never hear me again. I give you 48 hours to pay. I have a notice reading this letter, and the timer will work when you see this letter. Filing a complaint somewhere does not make sense because this email cannot be tracked like my bitcoin address. I do not make any mistakes.
If I find that you have shared this message with someone else, the video will be immediately distributed.
If you doubt that this is true, write to me and I will send an example of what I have: RmQn4Ul4Aj@highreed.xyz
got this on the 8th and today is the 14th so its obviously fake but any ideas where they could have gotten my email? i reported it on outlook of course, any things i should do or just ignore it lol
Lawrence Abrams - 5 years ago
Usually they are coming from data breaches or spam lists.